Table of Contents
Cyber Security for Internet of Things
Everyone loves their smart devices which are known as the Internet of Things(IoT). More than 24 billion of IoT devices and IoT applications exist today and more of them will increase by 2030. These gadgets are our favorites because they make life easy and enjoyable and also allow us to communicate with our loved ones and get the information more fastly.
Companies are also interested in these smart devices as they help them communicate with customers and manage important infrastructure.
What Is the Internet of Things (IoT) and How Does it Work?
IoT stands for “Internet of Things” which is all about connecting everyday devices to the Internet. IoT gadgets, which include things like your phone, refrigerator, and even your car, fall under this category.
Connected to the internet, the sensors talk to each other and share information. It’s like they’re all part of one big network. This makes our lives simpler and easier. IoT may be used for a variety of things from improving farming practices to making our homes smarter.
Top 10 IoT Devices
- Smartphones
- Smart Speakers
- Smart Thermostats
- Smart Lights
- Smart Cameras
- Smart Locks
- Smart Doorbells
- Smart Appliances
- Wearable Devices
- Smart TVs
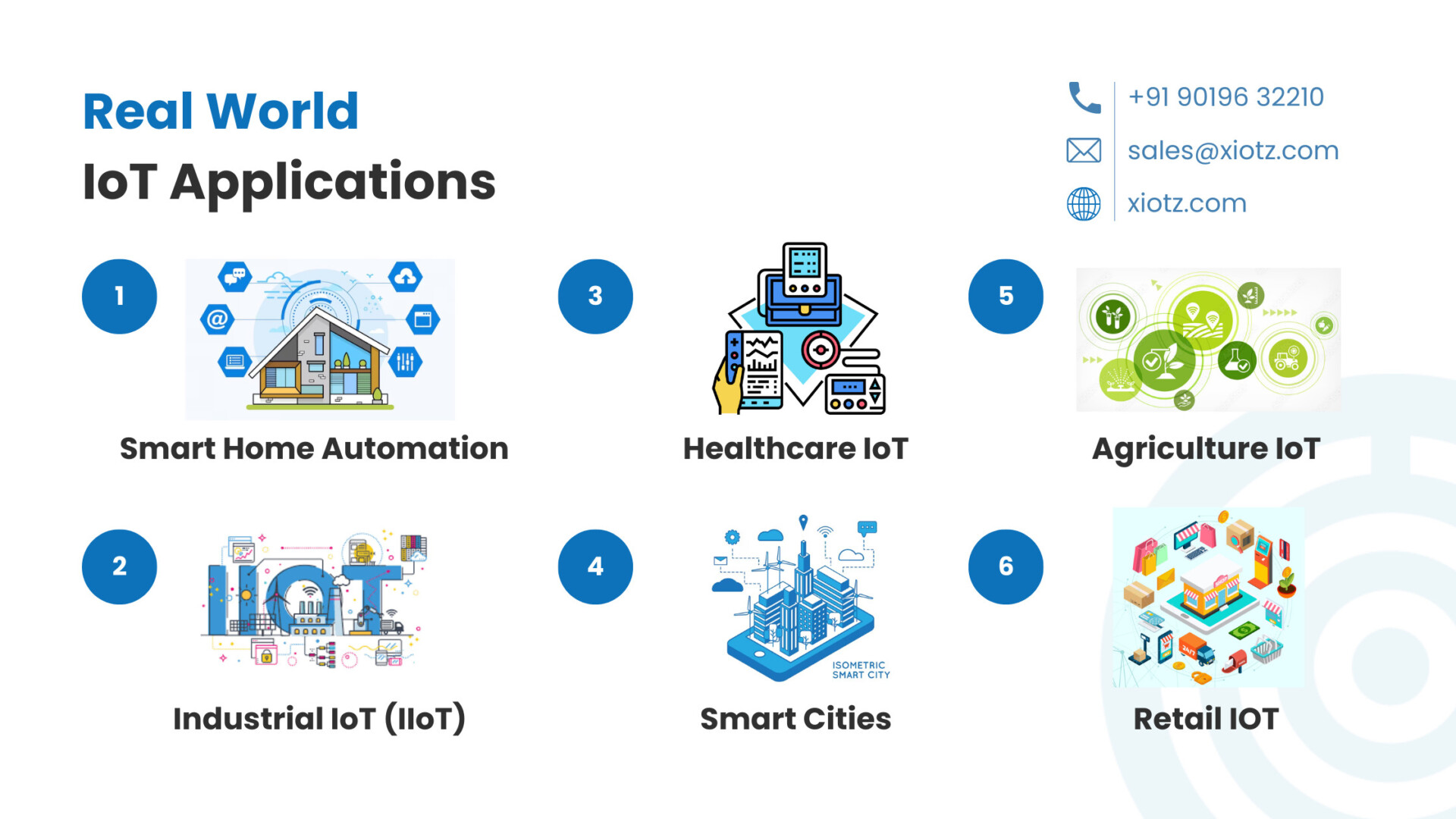
Top 10 Real-World IoT Applications in 2023
- Smart Home Automation
- Industrial IoT (IIoT)
- Healthcare IoT
- Smart Cities
- Agriculture IoT
- Wearable Health Devices
- Connected Cars
- Energy Management
- Environmental Monitoring
- Retail IoT
Why is IoT Security important?
IoT devices are built in unique ways and deal with large amounts of data, they can be at risk of cyberattacks. Sometimes, even simple IoT devices can be used to sneak up on a large network and cause problems. As a result of this, people became more aware of the significance of ensuring the security of IoT equipment.
We must be aware of potential flaws, data and security breaches, and other dangers when using IoT devices. Therefore, it is super important for companies to act aggressively for IoT security. This includes implementing security strategies and policies to mitigate the growing number of IoT vulnerabilities in today’s businesses.
How do IoT attacks occur?
IoT attacks occur when Cyber Criminals try to breach or harm smart devices connected to the internet.
Top 5 IoT attack vectors
- Weak passwords: Sometimes people don’t set up strong passwords for their IoT devices like cameras or thermostats. These passwords can easily be guessed or discovered by bad guys.
- Software deficiencies: IoT devices use software. If those systems have bugs or problems, hackers can exploit them.

- Insecure communication: Hackers can listen in or alter content if the way the device communicates with the Internet is not secure.
- Outdated software: If people do not update their device’s software, it can be vulnerable to attacks as it does not have the latest security controls and patches.
- Phishing: Hackers can trick people into giving them access to their IoT devices by pretending to be otherwise
5 Worst Examples of IoT Hacking and Vulnerabilities in Recorded History
Stuxnet:
Stuxnet was a highly developed computer worm made to specifically target nuclear devices. Unlike most cyberattacks, it physically damages machines in the real world. It infected Windows PCs and Siemens PLCs by exploiting multiple vulnerabilities including daily flaws which unusually exposed multiple vulnerabilities in a single attack surface.
Mirai:
Mirai sought IoT devices using ARC processors and simplified versions of Linux. Infected devices with default usernames and passwords. One of its most notable attacks targeted Dyn penetrating 100,000 IoT devices and curtailing internet activity.
Casino data breach:
A cyberattack on a casino operator affected pokies machines and hotel policies. The extent of the data breach including credit card information remains unclear. Cybersecurity experts expressed disappointment with the casino’s security and urged other companies to learn from the incident.
Jeep Exploit:
Security researchers remotely hacked a Jeep at high speed revealing weaknesses in its entertainment system, engine and brakes
Implantable medical devices:
Medtronic faced a cybersecurity issue with some of its implantable devices including one device that received a high-level vulnerability. These devices communicate wirelessly, potentially allowing unauthorized access to switching systems or surveillance systems. Implantable pacemaker devices are recalled and updated to enhance patient safety.
Top IoT Trends To Watch For In 2023
- Blockchain
- Smart Cities
- IoT Powered with 5G Technology
- Traffic Management
- IoT-Empowered AI Applications
- Digital Twins

- Voice Activated IoT Devices
- IoT Security
- Edge Computing
- virtual reality (VR) and augmented reality (AR)
Top 5 IoT Challenges in 2023 and How to Overcome Them
The Internet of Things (IoT) presents a number of difficulties but there are also ways to overcome them. Here are some of the key challenges and corresponding solutions in IoT.
- Security Challenges:
Challenge: IoT devices are vulnerable to cyberattacks making them attractive to hackers.
Solution: Implement strong security measures, encryption, authentication, and regular updates to protect IoT devices. Isolate IoT devices through network separation.
- Data Privacy Statement:
Challenge: Collecting too much data raises privacy concerns.
Solution: Anonymize and store data, establish clear policy on use, and obtain user consent. Comply with data protection laws.
- Contact information:
Challenge: IoT devices use different communication protocols which pose challenges in performance.
Solution: Adopt standardized protocols and use middleware platforms to bridge communication between devices.
- Scalability and Overview:
Challenge: Managing a large number of IoT devices.
Solution: Use device management platforms for planning, monitoring, and updating. Use scalable cloud-based solutions.
5. Power limitations:
Challenge: Many IoT devices run on limited battery power.
Solution: Improve energy efficiency through efficient design and use low-energy communication systems.
References:
Cybersecurity For The Internet of Things (IoT)
Quick Links:
Join our shared vision partnership
Related Blogs:
Cyber Awareness: Staying safe in digital world
The role of cybersecurity in the internet of things
Staying safe in the digital world
