xiotz TOC
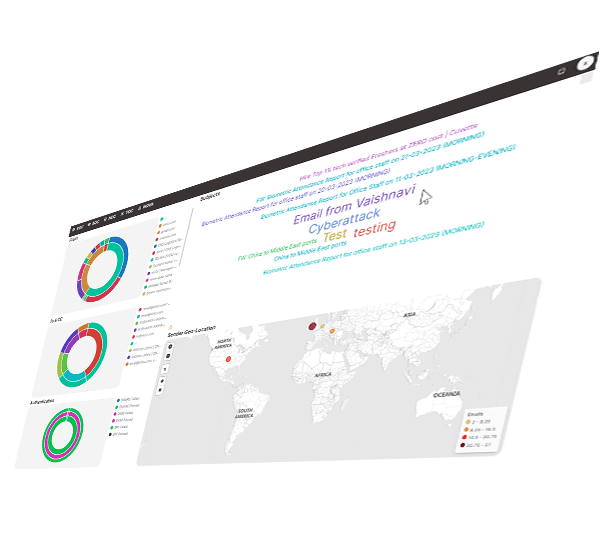
Threat
Operation Centre
|
Offensive-security with a team of ethical hackers verifying & validating the organization’s detection and response capabilities and provides security feedback
Decoys & Traps
Use a multi-layered deception approach to outwit adversaries by employing email, RDP, SSH, database, and network decoys in addition to app and system traps.
Email Analyzer
Email traps provide a complete solution to keep your inbox safe and data secured by adding a misleading layer and revealing hidden attackers.
Sinkhole DNS
With our DNS Sinkhole, you can protect your network against malware, backdoors, and botnets by rerouting access requests to harmful domains to a harmless black hole.
Decoys & Traps
- Network & system
- App & Database
- Email, RDP & SSH
- Mobile & Endpoint
more
Email Analyzer
- DMARC Analyzer
- DKIM Analyzer
- SFP Analyzer
- Email Traps
more
Sinkhole DNS
- Malware
- Backdoors
- Botnets
- Secure DNS
more
DECOYS & TRAPS
DECOYS & TRAPS
Intentionally vulnerable trap set up as a decoy to lure cyber attackers and detect, deflect and study hacking attempts to gain unauthorized access. The solution is built in with Network, System, Application, CMS, Database & Email decoys.
Intentionally vulnerable Network devices and systems setup as a decoy to lure cyber attackers and detect, deflect.
Application and Database trap setup to study and identify hacking attempts to gain unauthorized access, assist in a defensive network security posture.
Inactive EMail servers and RDP servers set up specifically as a tool to catch spammers red-handed as these servers are not in use.
End user mobile devices and laptops with known vulnerabilities are setup as landmines to identify the insider threat.
EMAIL ANALYZER
EMAIL ANALYZER
DMARC, DKIM, and SPF are email authentication protocols that help ensure the authenticity of emails and protect against email-based attacks such as phishing, spoofing, and spam. Deceptive email address are used to capture spam emails or malicious emails from hackers.
xIoTz DMARC Analyzer improves the email security posture and ensures that legitimate emails sent from their domain are not blocked or marked as spam by recipient email systems. Increases deliverability and helps identify potential phishing attacks or spoofing attempts.
With xIoTz XOC domain owners analyze DKIM signatures on their outgoing messages and identify any issues with their DKIM configuration.
DKIM Analyzer prevents email spoofing using Domain Key Identification verification & Validation.
Analyze the SPF records on the owner’s domain and identify any issues with their SPF configuration. Identifies domain’s SPF policy affecting email deliverability due to failed SPF checks.
Deceptive email addresses are used to capture spam emails or malicious emails from hackers. Email traps lookalike legitimate and attractive to spammers or hackers & monitored for suspicious activity by xIoTz Email Trap.
SINKHOLE DNS
SINKHOLE DNS
Blocking and Filtering malicious adware, spyware, ransomware, botnets, Trojans, Rootkits & Worms. Provides an authoritative secure DNS for the enterprise with custom website blocking.
Watch out! Malware like spyware (steals your secrets), adware (bombards you with ads), and ransomware (holds your files hostage) lurk online. Protect yourself with vigilance and security tools.
Be wary of hidden intruders! Trojans disguise themselves as harmless programs, rootkits burrow deep for stealthy control, worms slither through networks spreading chaos, and keyloggers silently steal your every keystroke. Stay vigilant and use strong defenses to keep these digital backdoors locked tight.
Botnets are like armies of hijacked devices controlled by malicious actors. Agobot, SDBot, SpyBot, and GT Bot are just a few examples of these “zombie armies” used for tasks like stealing data, launching attacks, or spamming. Stay safe online and avoid becoming part of this dark force!
Secure private authoritative DNS.
sneak and peek
xIoTz TOC
-

DMARC implementation significantly diminishes the risk of attackers spoofing your domain for phishing and impersonation attempts, protecting your users and data.
-

Improve email deliverability by ensuring only authorized sources send emails from your domain.
-

Safeguard your brand image from being misused in email-based scams.
-

Meet industry standards and regulations that mandate DMARC implementation.
-

Fortify your overall email security posture with DMARC as a critical layer.
-

Provides confidence by ensuring your network is continuously monitored and protected by a robust intrusion detection system, allowing you to focus on your core business objectives.
-

Unmask malicious actors and campaigns targeting your organization before they can launch an attack.
-
Strengthen your defenses against phishing attempts, spam emails, malware distribution, and other email-borne threats.
-

Decoys serve as attractive targets, luring attackers away from critical systems and enabling early detection of malicious activity.
-

By creating a maze of deceptive environments, you significantly complicate an attacker's ability to navigate your network and locate valuable assets.
-

Deceived attackers expend time and effort on fake systems, delaying their attempts to breach your real defenses.
-

Deception empowers you to test your security controls and identify weaknesses before attackers exploit them.
Values
Company Values
xloTz human rights policy applies to xloTz staff and partners. We also expect our suppliers, vendors, and customers to respect and adhere to.
Services
xIoTz Unified Cyber Assurance platform
xIoTz UCAP is a self-healing military grade solution built on an Edge-Cloud platform providing 30+ Security Products built-in & integrated with SIEM enabling cyber safety & data assurance.
Features
xIoTz Private Limited © 2025 | All Rights Reserved