Table of Contents
Introduction
Surviving without the internet is challenging for today’s generation. When we think of the word “internet”, what usually comes to mind are platforms like – Google, Instagram, Facebook, YouTube, etc. However the scope of the internet is not just limited to this. The Internet is like a space -” infinite”. Where your imagination stops, the dark side of the internet begins.
What is the dark web?
According to Britannica “The dark web is a part of the internet that exists on darknets, requiring specific software and configurations to access. It comprises websites not indexed by conventional search engines, allowing users to visit with complet
As of October 2023, “there were 5.3 billion internet users worldwide, which amounted to 65.7 percent of the global population. Of this total, 4.95 billion, or 61.4 percent of the world’s population were social media users.”
Out of this 5.3 billion people:
- 2 billion people are significantly active on Facebook.
- 3.7 million videos are uploaded daily on YouTube.
- Over 2.5 lakhs (250,000) websites are registered each day.
- Over 1 billion websites have been registered in total till date.
This data only represents the surface web which is significantly just a small part of the entire internet.
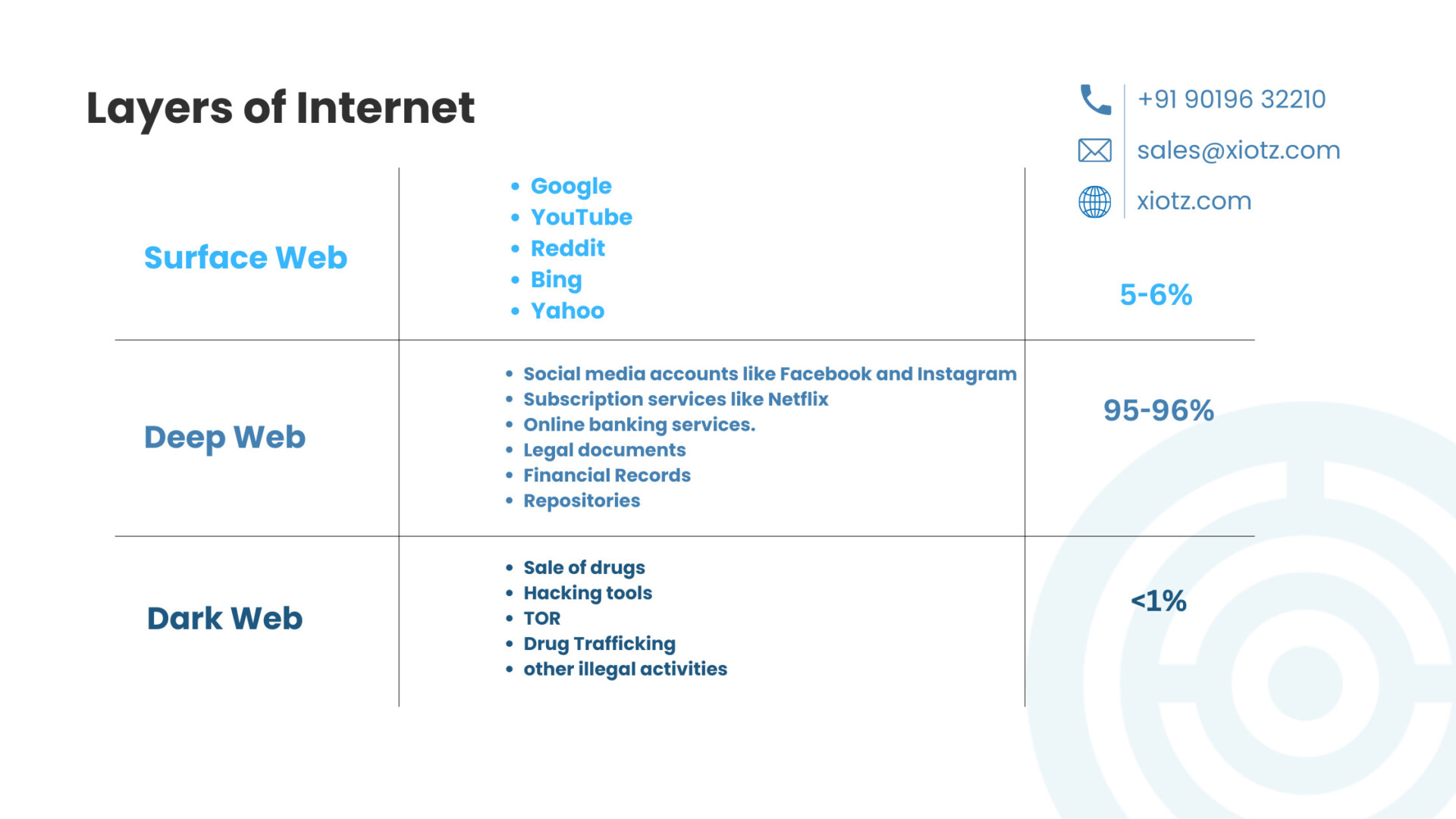
Layers of Internet – The Surface Web, The Deep Web and The Dark Web
There are 3 Layers of the Internet –
| Layers | Description | Part of Internet (%) |
| The Surface Web | This is the part of the internet that is easily accessible and searchable by normal search engines. The Surface Web is a part of www (world wide web) It includes websites and content that can be found through platforms like
| 5-6% |
| The Deep Web | The Deep Web refers to the major part of the internet that is not indexed by search engines. It includes password-protected websites, databases, and other content that is not meant to be publicly accessible. Examples include:
| 95-96% |
| The Dark Web | The Dark Web is a small and hidden part of the internet that requires special tools and software to access. It is known for its anonymity and privacy features. Transactions on the Dark Web are often conducted using cryptocurrencies like Bitcoin. While it is a place for some legitimate activities, it is also associated with illegal activities such as
Accessing the Dark Web requires specific software like Tor (The Onion Router). | <1% |
This website contains the list of all the activities on Dark Web – https://thehiddenwiki.org/
When exploring the dark web, we find that it represents only a small part of the vast internet landscape. As it is said, “Known is a drop, unknown is an ocean.” It means that what we know about the dark web is just a tiny bit compared to the huge amount we don’t know about the rest of the internet.
Evolution of Dark Web
In the 1960s, the concept of an anonymous online communication network originated with ARPANET(Advanced Research Projects Agency Network).
ARPANET was used to share information between computers without needing regular phone connections. Initially developed for academia, the military found utility during the Cold War, leading to government funding. ARPANET facilitated bold experiments, such as the first illegal online transaction in the early 1970s.
As time passed, ARPANET became more private, but researchers still had freedom to try new things. In the 1980s, the ARPANET split into two parts. One part was for the military, and the other became the basis for the internet we know today.
In the 1980s, the internet became popular. “Data havens” were created to store information with online safety. The 1990s marked the public release of the Internet, the Dot-Com Bubble, and the development of Tor, a private browsing network pivotal to the dark web’s growth.
In August of 1991, the Internet finally became publicly available.
In 2000, Freenet, a free software significantly for sharing files anonymously was released.
In 2002, Tor was developed particularly for letting people browse freely and anonymously. Tor was meant for good things, but it unintentionally became a place for illegal activities. It started in the 1990s, when researchers at the U.S. Naval Research Lab wanted a way to make internet traffic anonymous.
In 2008, they developed the Tor browser to make it easy for anyone to use. This led to the growth of the dark web with many illegal websites.
Bitcoin was released in 2009 and made illegal transactions on the dark web easier. The 2010s saw a rise in dark web activity, including during the Arab Spring, where Tor helped activists stay safe online.
In 2011, a popular dark web marketplace for illegal drugs was made known as Silk Road. The FBI shut down the Silk Road in 2013. Snowden’s whistleblowing in 2013 underscored Tor’s role in protecting against mass surveillance.
In 2015, Playpen, a dark website for child pornography was shut down. Even though there have been other events on the dark web, these are some of the important ones showing how it has changed over time.
Benefits of using Dark Web
- Users can specifically browse the dark web anonymously, protecting their identity and privacy.
- Particularly provides a platform for individuals to share their opinions without fear of censorship.
- Offers access to critical resources such as social media and blocked websites, especially in regions with restricted internet access.
- Tools like Tor protect individuals against mass surveillance so their online activities remain private.
- Facilitates whistleblowing by offering a secure environment for individuals to expose wrongdoing without fear of retribution.
- Uses encryption software and secure communication methods to stay secure and remain anonymous.
- Facilitates secure transactions with the use of cryptocurrencies which reduces the risk of fraud or identity theft.
Risk and Threats of Dark Web
- Identity Exposure: Increased risk of identity exposure due to the presence of malicious actors and criminals.
- Illegal Activities: Used for various illegal activities such as buying and selling of drugs, cybercrime and the selling of stolen data.
- Malware and Cyber Attacks: There’s a higher chance of getting viruses or being attacked by hackers when you visit certain websites on the dark web.
- Law Enforcement Operations: Risk of being caught in law enforcement operations targeting illegal activities on the dark web.

- Infection from Harmful Content: Possibility of encountering disturbing or harmful content, including illegal pornography or extremist materials.
- Financial Scams: Attackers might trick you into losing money when you’re on the dark web.
What can be found on the dark web?
- Illegal Marketplaces
- Drugs
- Weapons
- Stolen Data
- Hacking Tools
- Firearms
- Malware
- Fake Documents
- Cryptocurrency Scams
- Encrypted Email Services
- Anonymous Forums

How to access The Dark Web?
STEP 1: Connect to a safe VPN:
Before entering into the dark web, ensure your online security by connecting to a trustworthy Virtual Private Network (VPN). A VPN encrypts your internet connection by adding an extra layer of privacy and anonymity.
STEP 2: Download and Install the Tor Browser
The Tor Browser(an acronym for the “The Onion Router”) is the most popular and common tool for accessing the Dark Web. It was developed by the U.S Navy and made public in 2004. Tor Browser is based on Firefox and configured to protect your anonymity.
Download the Tor Browser from the official Tor Project website https://www.torproject.org/ ).
Follow the installation instructions provided on the website to set up the Tor Browser on your device.
STEP 3: Access the dark web with Tor Browser
Launch the Tor Browser after installation.
The Tor is a popular and most common browser that automatically connects to the Tor network, routing your internet traffic through a series of encrypted nodes to ensure anonymity.
Access Dark Web sites by entering their “.onion” URLs into the Tor Browser’s address bar. “.onion” is the special top-level domain used for Dark Web websites.
Understanding the concept of the Dark Net can vary as there are different top-level domains (TLDs) associated with various systems of anonymous internet access. Some examples include
- “.bit” for Zeronet
- “.i2p” for the Invisible Internet Project
- “.loki” for Loki
- “.onion” for the Tor Project
Each TLD corresponds to a specific platform within the realm of anonymous internet exploration.
STEP 4: Protect Your Identity:
While surfing on the dark web, take extra precautions to safeguard your identity and personal information.
Avoid sharing any personal details or using real names on dark web platforms.
Avoid downloading files from untrustworthy sources to prevent malware or other security threats.
Consider using additional privacy tools like secure messaging apps and encrypted email services to communicate anonymously.
Red Rooms on Dark Web
In the mysterious part of the internet called the Dark Web, there are stories about something called Red Rooms. These are said to be live videos showing really scary things like torture and murder. People can suggest what terrible thing should happen next, but they have to pay with a special kind of money called cryptocurrency, which is hard to trace. The person who pays the most gets to choose what happens.
The Dark Web is like a hidden world with around 2,000 secret websites. Regular search engines can’t find them. You need special tools, like Tor, to get in. It’s a place where people can stay anonymous while doing things they don’t want others to know about. But, compared to the big internet with over a billion sites, the Dark Web is pretty small.
The idea of Red Rooms has been around for a long time, maybe coming from movies like “The Shining” where “RED RUM” is written out in lipstick on a door. Later, the movie reveals that what is really being written is “MURDER” backwards. Another hypothesis of where Red Rooms got their name is from the 1983 horror film “Videodrome”. In this movie, torture is shown on live TV in a room painted red. But as you look into it, you start to wonder if Red Rooms are real. There’s a lot of talk about them but no solid proof.
Just when you think you might find a Red Room, the site suddenly goes away. Then, it comes back with a fake video, like a guy being fed bacon. It seems like the whole thing was a trick. This happens over and over, making you think that maybe Red Rooms are just made-up stories.
Some say people are too embarrassed to admit they watched Red Room videos. But that doesn’t make sense because people do mean things online without being ashamed. Also, if Red Rooms were real, wouldn’t the bad people get caught eventually? The FBI catches people doing bad stuff on the Dark Web, so it’s hard to believe that Red Rooms could stay hidden.
Even hackers who use their skills for good have looked into Dark Web sites, including Red Rooms, and found that they’re not real. One hacker named Ketulu found that these sites were not set up with good security.
So, in the end, it seems like Red Rooms might just be stories. Even though there are bad things happening online, it’s likely that Red Rooms are just a spooky legend, not something real.
Conclusion
In the world of the Dark Web, we discovered different layers and its history. There are things like the Surface Web, the Deep Web, and even mysterious Red Rooms. But as we explore, we find that some stories may just be myths. It’s like a cautionary tale – be careful and question what you hear online. Understanding this hidden part of the internet is important to stay safe in the digital world. So, be curious but be cautious too!
Related Blogs:
The Dark Side of Technology: Cyber Terrorism Attacks
Related Terms:
Related Links:
4 Myths About the Dark Web: Is It Really What You Think
Dark Web Facts Revealed: Myths and Stats About the Secret Web
Quick Links:
Inviting people to a partnership of mutual trust