Table of Contents
xIoTz Network Flow Management (NFM)
Introduction
NFM provides information about the network traffic, utilization, source and destination IP and ports.
xIoTz-AI engine maps the information with the Geo-location, IP reputation DB, Autonomous System and IANA databases to gain deep network insights, evaluate risk, bottlenecks and address them.
About xIoTz: Unified Cyber-Assurance Platform
xIoTz eXtented Operation Centre unifies the Network Operation center (NOC), Security operation center (SOC). Threat Operation Center (TOC) & NexGen Vulnerability Assessment (NGVA) in a single pane of glass.
xIoTz Security Operation Center (SOC) provides:
- Network Flow Management
- Network Intrusion Detection
- Network Behaviour Anomaly
- Endpoint Detection & Response and
- Web Application Firewall.
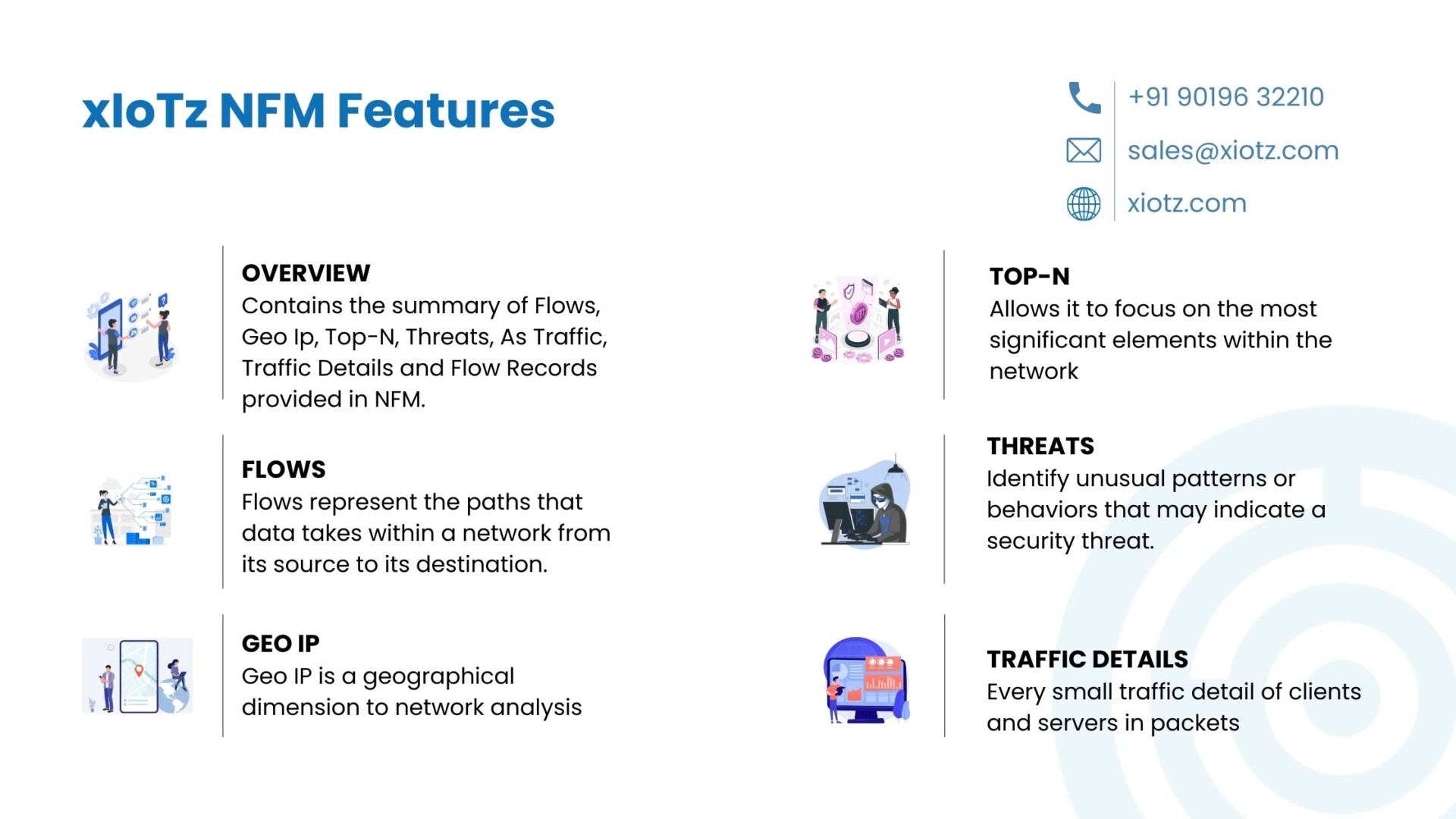
xIoTz NFM Features
OVERVIEW
The overview part contains the summary of Flows, Geo Ip, Top-N, Threats, As Traffic, Traffic Details and Flow Records provided in NFM.
FLOWS
Flows specifically represent the paths that data takes within a network from its source to its destination.
xIoTz NFM tracks and categorizes these flows into:
- Client and Servers
- Source and Destination
- NOT Source As Private and NOT Destination As Private
Moreover, this provides valuable insights into the data movement within the networks.
GEO IP
Geo IP is particularly geographical dimension to network analysis. By mapping the IP addresses of network traffic to physical locations, it’s easy to gain a comprehensive view of where the data is originating and where it’s headed.
xIoTz provides Geo IP of Client and Servers and Source and Destination in the form of:
- Graphs
- Maps and
- Tables
This geographical insight is invaluable for optimizing network routes, ensuring efficient data transfer, and identifying any anomalous or suspicious activity based on geographic patterns.
TOP-N
NFM Top-N feature allows it to focus on the most significant elements within the network. Whether it’s the top TALKERS, SERVICES AND CONVERSATIONS, this feature provides a concise and prioritized view of network activity.
Identifying the top contributors enables quick decision-making and resource allocation, enhancing overall network efficiency.
THREATS
By analyzing network flows, NFM can identify unusual patterns or behaviors that may indicate a security threat. From spikes in data transfer to unexpected connections, NFM serves as a frontline defense against potential cyber threats, allowing for swift response and mitigation.
AS TRAFFIC
Understanding Autonomous System (AS) traffic is essential for organizations with complex network architectures. NFM provides insights into traffic patterns between:
- Source Autonomous Systems (bits/s)
- Source Autonomous Systems (pkts/s)
- Destination Autonomous Systems (bits/s)
- Destination Autonomous Systems (pkts/s)
This facilitates better network planning and interconnection management.
TRAFFIC DETAILS
NFM provides every small traffic detail of clients and servers in packets, flow records and bits. xIoTz also provides the functionality to classify Traffic Details on the basis of:
- Types
- Attributes and
- Locality.
This level of detail is important in troubleshooting network issues, optimizing resource allocation, and ensuring the overall health of the network.
FLOW RECORDS
Flow records serve as a comprehensive log of network activity, particularly detailing every interaction within the network. These records not only aid in historical analysis specifically but also play a vital role in compliance, enabling organizations to meet regulatory requirements and conduct forensic investigations when needed.
Benefits of xIoTz NFM
- Real-Time Monitoring: Provides immediate visibility specifically into network activity, enabling quick detection of anomalies and security threats.
- SIEM Built-In & Integrated: Integrates with Security Information and Event Management (SIEM) systems for comprehensive security monitoring as well as threat correlation.
- Event Logging: Captures detailed logs of network activities and security events, further facilitating forensic analysis and compliance audits.
- Periodic Reporting: Generates regular reports summarizing network performance, utilization, and security incidents, thus aiding in decision-making.
- Automated Alerts & Notifications: Sends automated alerts for specific events, thus allowing proactive responses to potential issues and minimizing downtime.
- Resource Utilization: NFM helps in better utilization specifically of network resources. It ensures that bandwidth is allocated appropriately, further preventing congestion and bottlenecks.
- Network Visibility: NFM provides insights into network traffic patterns, helping administrators identify issues, analyze performance, and make informed decisions about network optimization and upgrades.
Industry Use-Cases
- Telecommunications: Ensure optimal bandwidth allocation, monitor network traffic, and identify potential bottlenecks for seamless communication.
- Healthcare: Safeguard patient data by monitoring and securing network flows, ensuring compliance with regulatory requirements.
- Finance: Detects and mitigate security threats as well as optimize data transfer, and ensure secure financial transactions within complex networks.
- Manufacturing: Enhance operational efficiency by tracking and optimizing the flow of data between machines, systems, and production units.
- Education: Manage bandwidth effectively as well as secure sensitive student information, and ensure reliable connectivity for online learning platforms.
Conclusion
xIoTz Network Flow Management helps in achieving optimal network performance, security, and responsiveness through features like real-time monitoring, SIEM integration, event logging, periodic reporting and automated alerts to stay secure in a digital environment.
Elevate Your Cybersecurity Defense with xIoTz Network Flow Management
Don’t let your organization particularly be a victim of cyber threats. Embrace the future of cyber assurance with significantly xIoTz. Safeguard your business, protect sensitive data, and ensure a secure digital environment for your team.
Get Started Today
Visit xiotz.com to explore the full suite of xIoTz cyber assurance solutions. Take the first step towards a resilient and secure digital future.
Empower your business with xIoTz – Seamless Networks and Secured Flows..
Related Blogs:
Network Intrusion Detection system
Related Terms:
Reference Links:
Network Intrusion Detection System