Table of Contents
xIoTz Network Intrusion Detection System (NIDS)
A Network Intrusion Detection System (NIDS) specifically checks the flow of information in a computer network to find and stop bad things from happening. It helps keep a company’s network safe from harmful actions like attacks, further scanning for weak spots, and overwhelming the network so it can’t function properly.
Network protection
xIoTz NIDS monitors network traffic for following activities such as malicious activity, security policy violations and protects organizations by detecting and responding to network threats.
- Signature-Based Detection: Signature-based detection specifically helps to recognize harmful things like viruses and malware by looking for specifically known patterns of bad behavior.
- Anomaly-Based Detection: Anomaly-based detection is like a watchful eye that looks for strange or unusual behavior in the network. It generally helps identify weird patterns and activities that don’t fit the usual way things happen.
- Packet Capture And Analysis: NIDSS watches and understands network data as it happens to figure out where the data is coming from and to catch anything that seems strange or suspicious.
- Customized Policies & Rules: Specialized particularly warnings and custom rules for the organization help make sure we don’t get too many wrong alerts about problems that aren’t really there.
- Machine Learning And AI: xIoTz NIDS particularly use machine learning and Al algorithms to identify unknown zero-day attacks and threats.
- Forensics & Investigation: Cyber investigation and identification of the source & forget of the attack based on historical incidents and log retentions.
- Real-Time Monitoring: xIoTz NIDS monitor network traffic in real-time quickly detect and respond to security threats.
- IOA and IOC: xIoTz NIDS use Indicators of Attack (IOA) to proactively identify potential threats and Indicators of Compromise (IOC) to pinpoint evidence of successful cyber attacks, enabling swift response and mitigation.
- SIEM Built-In & Integrated: xIoTz NIOSs comes ready to work with Security Information and Event Management (SIEM) to make it simple for automation and coordination.
- Event Logging: xIoTz NIDS keeps a record of events and makes reports to recognize patterns of activities that seem suspicious.
- Automated Alerts & Notifications: xIoTz NIDS sends automatic warnings and messages specifically when it sees something not right or a possible security problem.
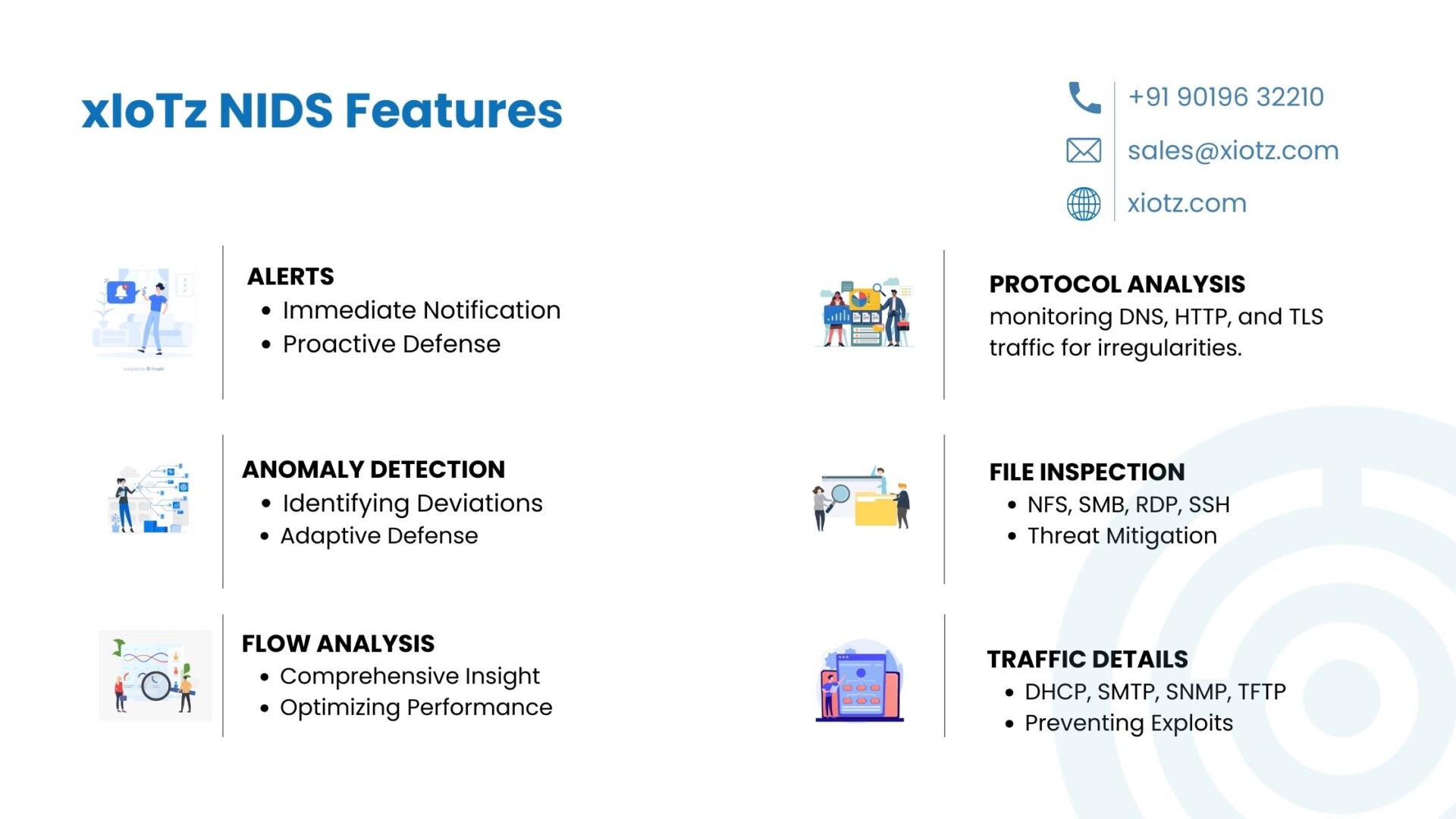
xIoTz NIDS Features
1. ALERTS
- Immediate Notification: NIDS rapidly sends warnings when it notices specifically suspicious happening in the network.
- Proactive Defense: Helps security teams quickly deal with possible threats before they become a problem.
2. ANOMALY DETECTION
- Identifying Deviations: NIDS uses anomaly detection to find strange patterns in how the network normally behaves.
- Adaptive Defense: Helps find and deal with new threats before they become a problem, even if we haven’t seen them before.
3. FLOW ANALYSIS
- Comprehensive Insight: NIDS studies how data moves in the network to get a full picture of the patterns it follows.
- Optimizing Performance: Helps make the network work better and finds places where it might slow down.
4. PROTOCOL ANALYSIS
DNS, HTTP, TLS: NIDS delves into protocol-specific analysis, monitoring DNS, HTTP, and TLS traffic for irregularities. It is ensured that these critical protocols are followed to expected behaviors for enhanced security
5. FILE INSPECTION
- NFS, SMB, RDP, SSH: NIDS scrutinizes file-related protocols like NFS, SMB, RDP, and SSH.
- Threat Mitigation: Identifies suspicious file activities, protecting against unauthorized access and potential malware threats.
6. APPLICATION LAYER PROTOCOLS
- DHCP, SMTP, SNMP, TFTP: NIDS monitors application layer protocols like DHCP, SMTP, SNMP, and TFTP.
- Preventing Exploits: Enhances security by identifying irregularities in these protocols, preventing potential exploits.
7. ADVANCED PROTOCOLS
- IKEv2, DNP3, KRB5, MQTT: NIDS extends its reach to advanced protocols, including IKEv2, DNP3, KRB5, and MQTT.
- Comprehensive Defense: Ensures a robust defense against sophisticated attacks targeting these protocols.
8. SPECIALIZED PROTOCOLS
- RFB, SIP, FTP, RPC: NIDS covers specialized protocols such as RFB, SIP, FTP, and RPC.
- Maintaining Security: Provides insights into potential security risks associated with these specialized protocols.
9. STATISTICAL ANALYSIS
NIDS uses math to watch how the network usually acts. This helps predict if something bad might happen, so we can stop it before it gets worse.
10. OVERVIEW
Overview is nothing but the summary of all the NIDS features that contain Protocols, All Events, Anomaly – Events, Alert Signatures, Countries, Anomaly – Protocols – Events, Alerts – Protocol – Categories.
Top 10 NIDS Benefits
xIoTz network intrusion detection system provides a wide range of benefits to increase the enterprise network security posture and the benefits are:
- Real-Time Threat Detection: Finds and deals with network threats right away, quickly spotting and stopping possible security problems.
- Improved Network Visibility: Greater visibility into enterprise networks, thus identifying potential security weaknesses, vulnerabilities and threats.
- Early Warning Of Attacks: Proactive measures to prevent and mitigate the impact of the attack by specifically Providing early warning of potential cyber threat.
- Reduced Response Times: Automated detection and response to security threats, reduce response times and minimize the impact of security incidents.
- Customized Rules & Policies: Customized to meet organization specific security needs and tailored security policies addressing unique requirements.
- Compliance & Standards: Provide regulatory compliances and industry requirements mandated by HIPAA as well as PCI-DSS standards.
- Reduced Security Risks: Continuous monitoring and threat detection, to prevent costly security breaches and improves organization security posture.
- Improved Incident Response: Investigate past security incidents, identify the source of the attack and take proactive steps to prevent future incidents.
- Continuous Monitoring: NIDS operates 24/7, providing continuous monitoring and protection against a wide range of security threats.
- Logging and Alerting: NIDS generates logs and alerts for security events, providing valuable information for security administrators to investigate and respond to potential threats.
Industry use-cases
- Financial Services: NIDS in financial services ensures the real-time detection of suspicious activities, safeguarding transactions and customer data against cyber threats, thereby maintaining the integrity of financial operations.
- Healthcare Providers: In healthcare, NIDS is crucial for protecting patient information. It quickly spots and deals with any unauthorized attempts to access records, making sure the healthcare provider follows strict rules like HIPAA, and making overall data security stronger.
- E-commerce Platforms: Safeguarding e-commerce transactions, NIDS is vital for detecting and mitigating threats like SQL injection and DDoS attacks, ensuring the secure processing of customer payments and also preserving the integrity of online transactions.
- Manufacturing and Industrial Systems: NIDS offers continuous monitoring in industrial settings, identifying anomalies in network traffic to protect critical systems. This helps prevent cyber threats from disrupting operations and ensures the safety of industrial control systems.
- Government and Public Services: In government sectors, NIDS is essential for securing sensitive data and citizen information. It detects and responds to cyber threats, thus ensuring the availability and security of online services while meeting compliance standards and safeguarding public trust.

Conclusion
In conclusion, xIoTz network intrusion detection system keeps the company safe by finding and dealing with possible security problems quickly and effectively, further making the organization’s network security better.
xIoTz NIDS has lots of benefits and features, thus making it an essential component of the organization’s cybersecurity infrastructure.
Related Terms:
Network Intrusion Detection System
Related Blogs:
Reference links:
What is Network Intrusion Detection System (NIDS)?
NIDS | Network Intrusion Detection System | Redscan
NIDS – A Guide To Network Intrusion Detection Systems