Table of Contents
CERT-In’s 6-Hour Rule: Non-Compliance Isn’t an Option
A ransomware attack hits your servers at 2:00 AM.
Your team discovers it at 8:00 AM.
By 2:00 PM that same day — before most businesses have even started their incident response process — you must have already filed a formal report with CERT-In.
That’s the 6-hour rule. And most Indian businesses have no idea it applies to them.
This isn’t a guideline. It isn’t a best practice. It’s a legally enforceable mandate under the Information Technology Act, 2000 — with penalties that can shut a business down. ₹1 crore in fines. Up to one year of imprisonment for responsible officers. Disqualification from government tenders.
For an MSME, that isn’t a setback. That’s the end.
What Is CERT-In — And Why Does It Have This Kind of Power?
CERT-In is India’s national nodal agency for cybersecurity, operating under Section 70B of the Information Technology Act, 2000. Think of it as India’s cyber incident headquarters — part watchdog, part emergency response unit.
On 28 April 2022, CERT-In issued its landmark Cyber Security Directions, which came into full force on 28 June 2022. These directions dramatically expanded mandatory reporting scope and introduced the strict 6-hour window that now governs incident response across the country.
In 2025, CERT-In raised the bar further — issuing Comprehensive Cybersecurity Audit Guidelines and the dedicated 15 Elemental Cyber Defense Controls for MSMEs. The compliance bar isn’t staying where it is. It’s rising.
India vs. The World: How Strict Is the 6-Hour Rule?
Six hours.
Not 72 hours like the EU. Not 72 hours like the US. Six hours — from the moment anyone in your organization becomes aware of an incident.
The difference isn’t arbitrary.
The EU’s 72-hour window was deliberately designed to avoid overwhelming regulators with reports Thoropass — built around large enterprises with legal teams and compliance officers who need time to assess, confirm, and document before filing.
The US framework came after the Colonial Pipeline ransomware attack in 2021, when policymakers realized the government had no timely visibility into major cyber incidents hitting critical infrastructure. Cloudstar So they built a 72-hour window for incidents — and a tighter 24-hour window specifically for ransomware payments.
India took a harder line.
CERT-In’s 6-hour mandate isn’t about documentation. It’s about containment. The faster an incident is reported, the faster CERT-In can warn other businesses, identify attack patterns, and stop one breach from becoming ten.
The EU assumed enterprises need time to confirm. India decided that waiting to confirm is how a contained incident becomes a catastrophe.
Most businesses spend the first 24 hours just figuring out what happened.
Under CERT-In rules, that approach guarantees non-compliance.
The Compliance Trap Most Businesses Fall Into
Here’s the most dangerous misconception about the 6-hour rule:
“We’ll report once we know exactly what happened.”
That’s not how it works.
The clock starts the moment anyone in your organization becomes aware of an incident — not when you’ve confirmed it, not when legal has reviewed it, not when the board is briefed.
You report what you know. You investigate in parallel. The report comes first.
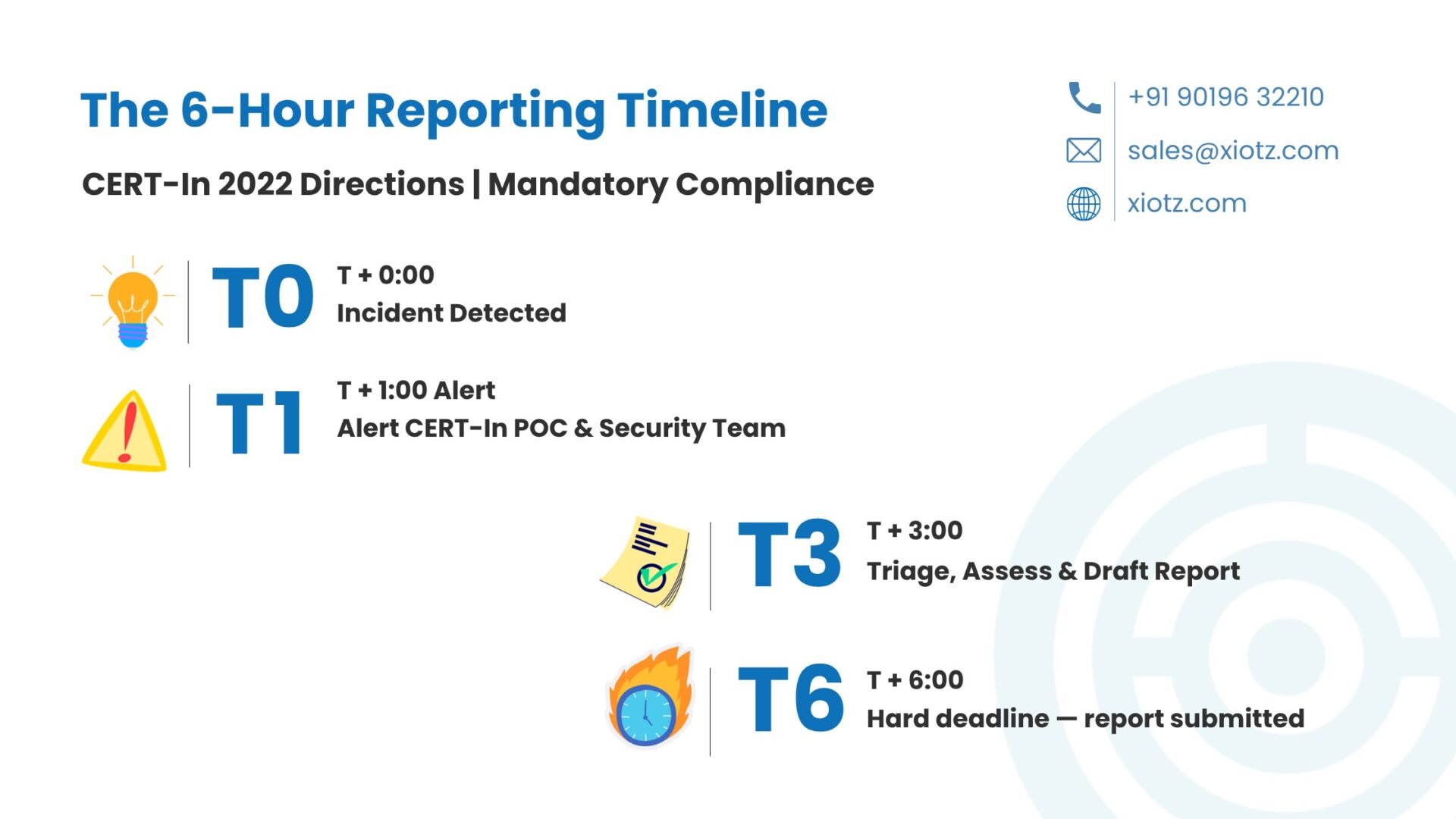
The 6-hour timeline in practice:
There is no grace period. There is no extension. There is no “we were still investigating.”
Who Does This Apply To?
If your business operates in India — or serves Indian users — you are almost certainly in scope.
CERT-In’s directions apply to:
- Service Providers — internet, telecom, cloud, SaaS, hosting
- Intermediaries — social media platforms, e-commerce marketplaces
- Data Centres — including colocation and managed hosting
- Body Corporates — any registered company handling data or IT systems
- Government Organisations — central and state government bodies
- VPN / VPS / Cloud Providers — subject to additional KYC and data retention rules
- MSMEs — explicitly brought into scope from September 2025
There are no revenue-based exemptions. No employee-count thresholds. If you have a server, an email system, and customers in India — you’re in scope.
Do You Fall Under CERT-In's 6-Hour Rule?
If you have a server, an email system, and customers in India — you're almost certainly in scope. Check your CERT-In readiness in 2 minutes and know exactly where you stand.
Check My ReadinessWhat Incidents Must Be Reported?
Any cyber incident that affects the availability, integrity, or confidentiality of your systems in any meaningful way is reportable. When in doubt — report.
Common examples include:
- Ransomware attacks — the fastest-growing threat facing Indian MSMEs
- Data breach — unauthorized access or theft of sensitive business or customer data
- Phishing and spoofing — social engineering attacks impersonating legitimate entities
- Malware — viruses, trojans, crypto miners, spyware
- DDoS attacks — disrupting the availability of your systems
- Website defacement — unauthorized changes to websites or insertion of malicious code
- Supply chain compromise — attacks via third-party vendors or software dependencies
- Unauthorised access — intrusion into IT systems, servers, or databases
If the incident affects your business in any meaningful way — file the report. You can follow up with additional details as the investigation progresses.
How to Report: Step by Step
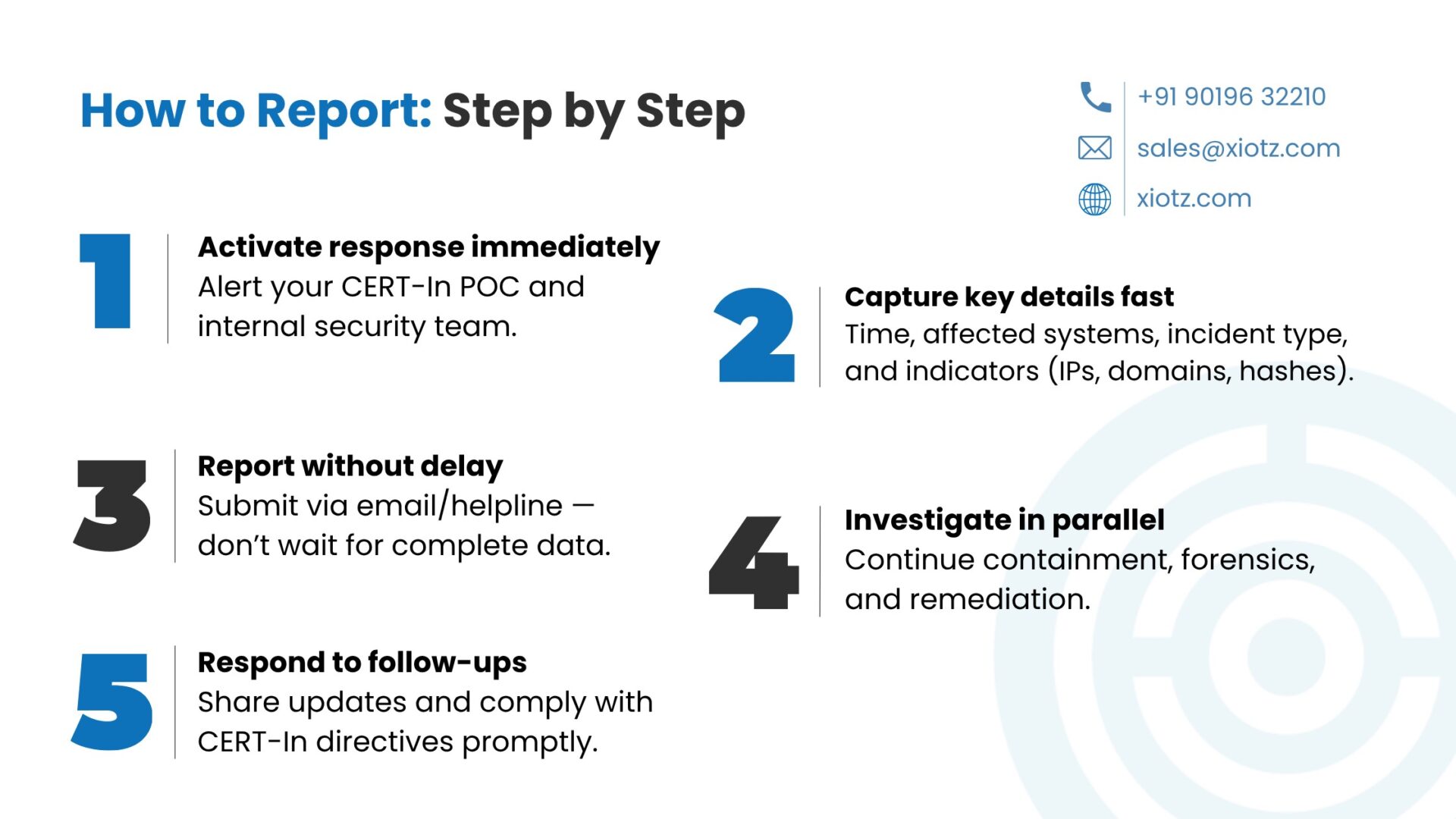
Step 1 — Activate your incident response plan Alert your designated CERT-In Point of Contact and your internal security team immediately. Every minute counts.
Step 2 — Gather initial facts Document the detection timestamp with timezone, affected systems, type of incident, indicators observed — IPs, hashes, domains — and steps already taken for containment.
Step 3 — Submit the report to CERT-In:
- Email: incident@cert-in.org.in
- Helpline: 1800-11-4949
- Fax: 1800-11-6969
Include all known details. Do not wait for perfection. An incomplete report filed on time is always better than a complete report filed late.
Step 4 — Continue investigation in parallel Reporting doesn’t pause your response. Continue forensic investigation, containment, and eradication while following up with CERT-In as new facts emerge.
Step 5 — Comply with follow-up requests CERT-In will review your report and may request additional information or issue directions. Comply within the specified timeframe.
CERT-In Compliance Is More Than the 6-Hour Rule
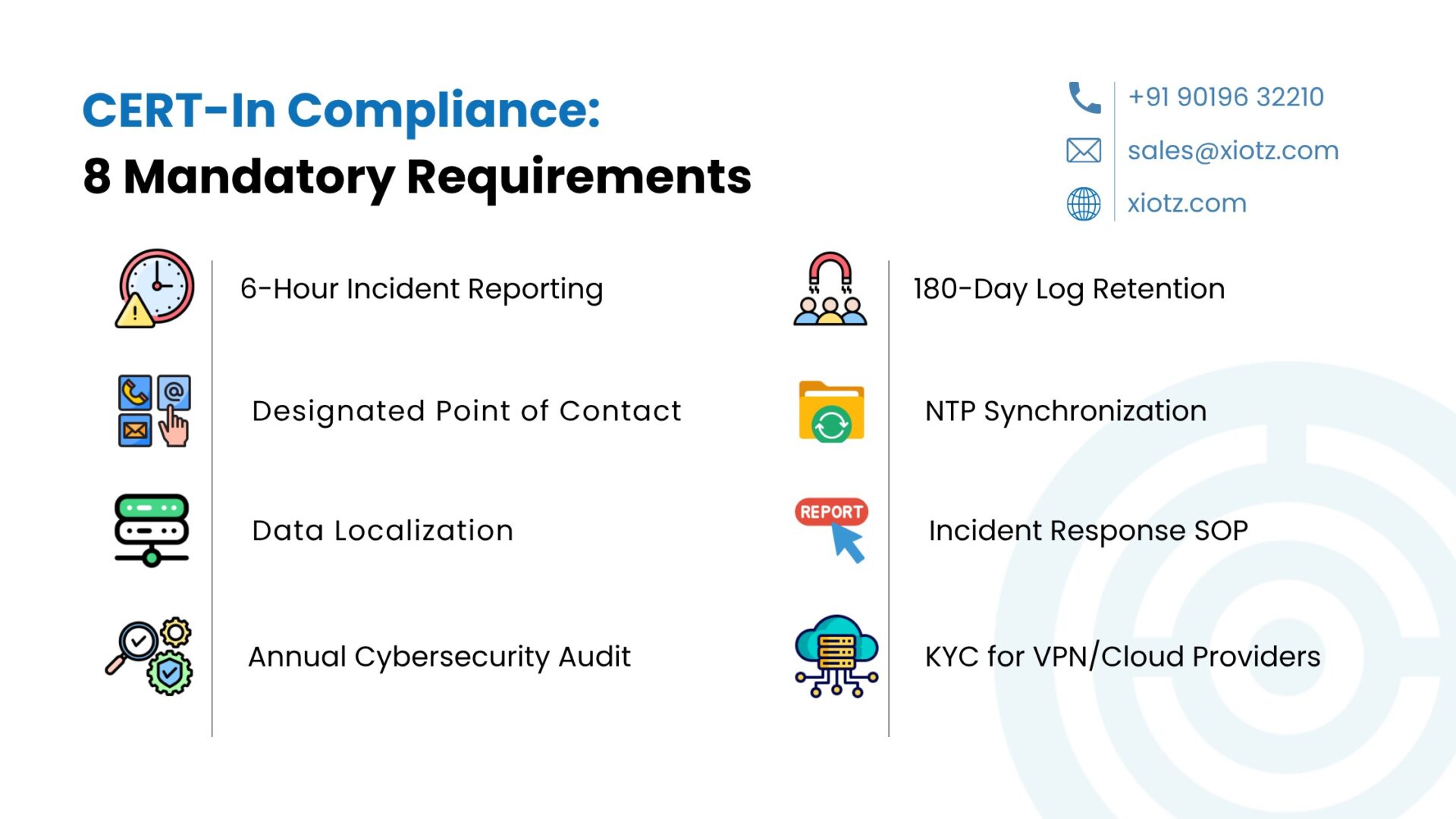
The 6-hour rule gets the headlines. But full CERT-In compliance is a layered obligation:
Requirement | What It Means |
6-Hour Incident Reporting | Report any cyber incident within 6 hours of detection |
180-Day Log Retention | Maintain ICT logs for 180 days, stored within India |
Designated Point of Contact | Named officer responsible for CERT-In communications, available 24×7 |
NTP Synchronization | Sync all system clocks with Indian NTP servers |
Annual Cybersecurity Audit | Conducted by a CERT-In empaneled auditor |
KYC for VPN/Cloud Providers | Validated subscriber data retained for 5 years |
Data Localization | Critical logs and subscriber data must remain within Indian territory |
Incident Response SOP | Written, tested response plan aligned to CERT-In reporting categories |
Miss any one of these — not just the 6-hour rule — and you’re non-compliant.
Your Business CERT-In Compliant? Find Out Now.
Most MSMEs discover compliance gaps during an audit — or after a breach. Use this free checklist to assess where your business stands against all 8 CERT-In requirements and the 15 Elemental Cyber Defense Controls — before it costs you ₹1 crore.
Download Free ChecklistThe MSME Wake-Up Call: September 2025
On September 1, 2025, CERT-In issued its dedicated framework for India’s MSME sector — the 15 Elemental Cyber Defense Controls (Guideline No. CISG-2025-03).
For the first time, millions of small businesses were explicitly brought into India’s formal cyber security compliance regime.
The reason is stark. MSMEs contribute nearly one-third of India’s GDP. A data breach in a small supplier becomes the backdoor into a much larger enterprise. India’s digital economy is only as strong as its weakest link — and for too long, that weakest link has been the unprotected small business.
xIoTz contributed directly to shaping this framework. We’ve seen what breaks. We’ve seen what survives. The 15 controls reflect that reality.
What Happens If You Don’t Comply?
Non-compliance with CERT-In directions isn’t a minor administrative issue:
Consequence | Impact |
Financial Fine | Up to ₹1 Crore |
Imprisonment | Up to 1 year for responsible officers |
Government Tenders | Disqualification |
IT Privileges | Suspension risk |
Reputational Damage | Customer trust — gone |
For an MSME, a ₹1 crore penalty isn’t a setback. It’s a shutdown.
The enforcement process begins with a report from a CERT-In officer, reviewed by a committee, leading to a complaint filed by the Director General of CERT-In with the court. This is not a theoretical risk. It is a real, enforceable process.
Don't Let a ₹1 Crore Fine Be Your Wake-Up Call.
Imprisonment. Fines. Disqualification from government contracts. The cost of non-compliance is real — and permanent. Book a free CERT-In compliance assessment with xIoTz and find out exactly what needs fixing before an auditor does.
Book Free AssessmentBuilding a CERT-In-Ready Organization
Meeting the 6-hour deadline is impossible with manual, ad hoc processes. Here’s how to build lasting compliance capability:
- Appoint your CERT-In Point of Contact A specific named officer — with a named alternate — responsible for all CERT-In communications. Reachable 24×7. Not just during business hours.
- Implement centralized log management All ICT system logs aggregated in one place. Retained for 180 days within Indian jurisdiction. Critical log sources on tamper-resistant storage.
- Automate incident detection Human detection is too slow for a 6-hour window. Endpoint detection, AI-powered email security, automated alerting — every minute of detection delay eats into your reporting window.
- Synchronize system clocks All servers, workstations, and network devices synced with Indian NTP servers — time.nplindia.org or samay.nic.in. Accurate timestamps are critical for incident timelines.
- Build a ready-to-use reporting template When a ransomware attack hits at 2:00 AM, you shouldn’t be drafting a report from scratch. Prepare the template now. Run a tabletop exercise at least once a year.
- Train your people Every employee who could detect — or be targeted in — a cyber attack needs regular training. CERT-In’s MSME guidelines mandate this at least twice a year. Make it practical, not just compliance theater.
- Conduct annual audits Engage a CERT-In empaneled auditor annually. Use it as a genuine stress test — not just a checkbox. Board-level visibility is not optional.
One More Layer: The DPDP Act Is Coming
India is in a period of rapid regulatory evolution.
With the Digital Personal Data Protection Act coming into force, organizations are moving toward a dual reporting obligation in the event of a personal data breach — one report to CERT-In within 6 hours, and another to the Data Protection Board of India once that framework is fully operational.
For sector-regulated entities, the complexity multiplies further. Banks report to RBI within 2–6 hours. Insurance companies notify IRDAI within 48 hours.
The practical implication is straightforward: build one unified incident response process that triggers parallel reporting workflows. Not separate siloed processes for each regulator.
The Cost of Building Compliance Is Far Lower Than the Cost of a Breach
CERT-In’s 6-hour rule is one of the strictest cyber security compliance mandates in the world. It exists because India’s government understands something many business owners haven’t accepted yet:
Cyber-attacks in India are not a future risk. They are a present reality.
Ransomware. Data breach. Phishing. Supply chain compromises. These happen every day, to businesses exactly like yours.
The 6-hour rule doesn’t exist to punish businesses. It exists because speed is the difference between a contained incident and a catastrophic one.
Start with the basics. Appoint your Point of Contact. Enable your logs. Build your reporting template. Train your team.
Then layer the rest.
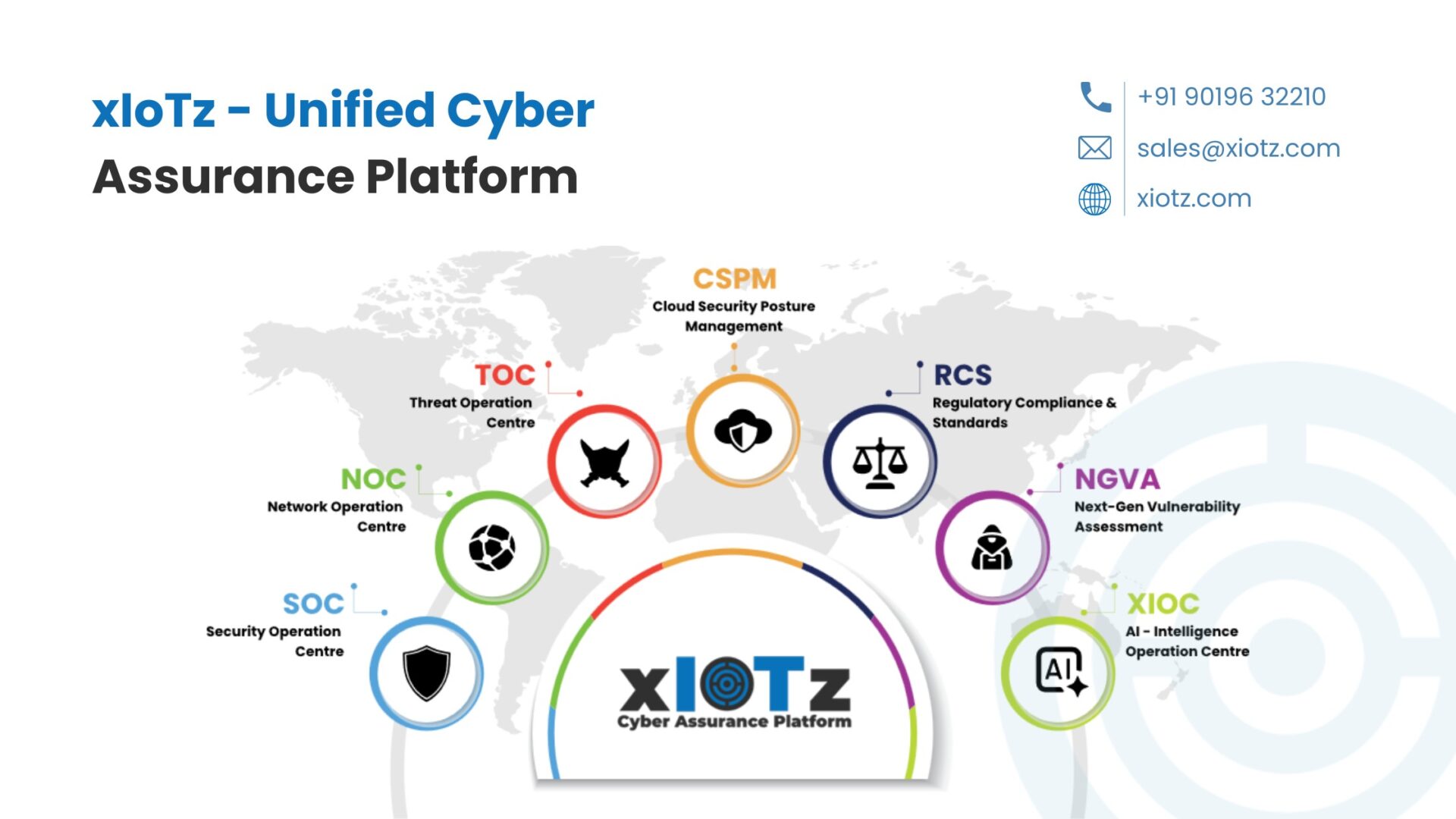
xIoTz Unified Cyber Assurance was built for exactly this — a single platform that gives MSMEs the monitoring, logging, incident detection, and audit-ready compliance they need to meet CERT-In requirements without building an internal security team from scratch.
Because the question was never whether a cyber-attack in India would happen.
The question is whether you’ll be ready when it does.
The 6-Hour Clock Doesn't Wait. Neither Should You.
xIoTz Unified Cyber Assurance gives MSMEs everything they need to meet CERT-In's 6-hour reporting rule — automated detection, centralized logging, audit-ready documentation, and a compliance dashboard that never sleeps. No internal security team required.
Book ConsultationLearn CERT-In ComplianceBlogs
Latest Posts & News
- Awareness
- Celebrations
- Education
- Event
- Experience
- Newsroom
- Opportunities
- Uncategorized
- Web Stories
- xIoTz Features

xIoTz helped shape India's CERT-In compliance framework. Here's the practitioner's checklist — all 15 controls, the penalties most businesses don't know about, and how to...

India's 63 million MSMEs finally have a cybersecurity baseline. xIoTz has contributed to the National Cybersecurity Framework for MSMEs — specifically the 15 Elemental Cyber...

xIoTz Private Limited has been named the winner of a national defence innovation challenge for developing an indigenous Security Information and Event Management (SIEM) solution...
Services
xIoTz Unified Cyber Assurance platform
xIoTz UCAP is a self-healing military grade solution built on an Edge-Cloud platform providing 30+ Security Products built-in & integrated with SIEM enabling cyber safety & data assurance.